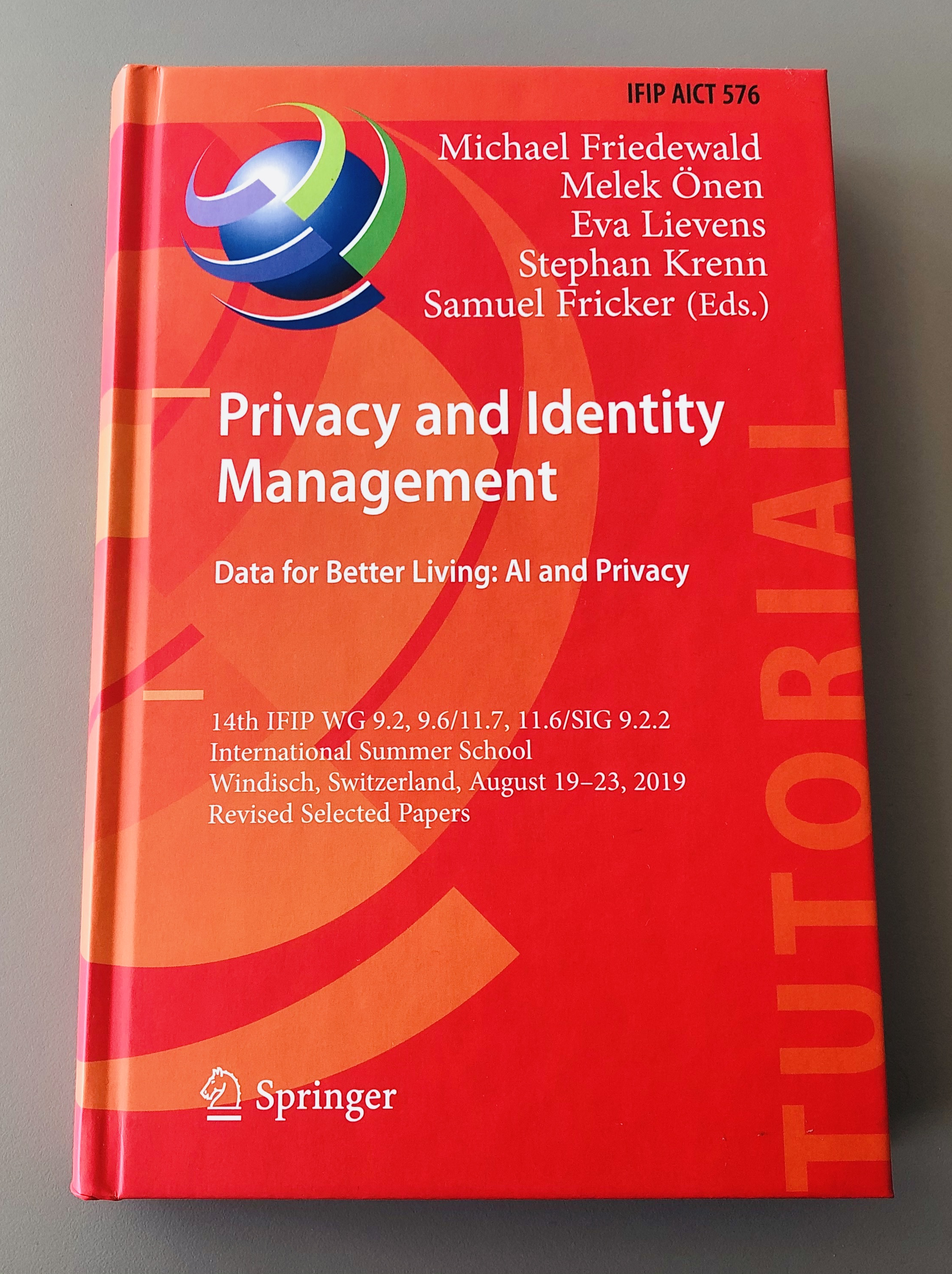
This week, between August 19-23 2019, I was in Switzerland attending the International Federation for Information Processing (IFIP) Summer School at the University of Applied Sciences Northwestern Switzerland (FHNW) in Brugg/Windisch. Attending this school is of great benefit to strengthen your network of professional and academic contacts, especially for those working on Information Privacy. Topics covered in the jam-packed schedule included: the ethics of Artificial Intelligence, sensors and biometrics, privacy by design (PbD), identity management, users and usability, and more.
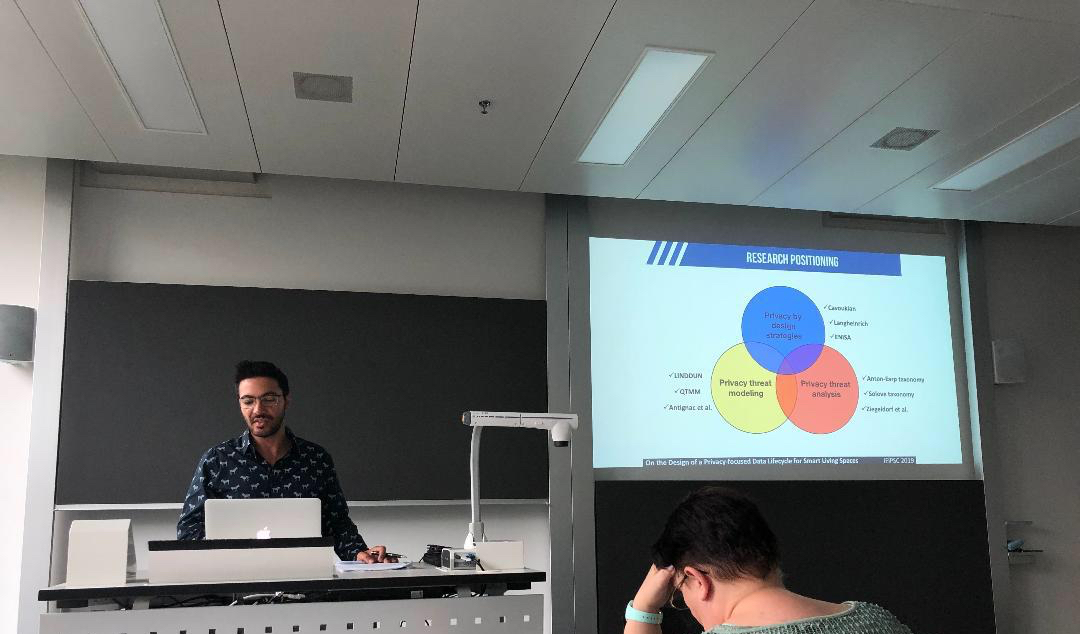
On Tuesday 20, I presented my paper therein titled: “On the Design of a Privacy-Preserving Data Lifecycle for Smart Living Spaces” in the “Privacy by Design” track. I had a 30 mins presentation slot and following that a 10 mins critical review from two pre-assigned paper discussants including questions from the attendees. I have to say that I have received very positive and constructive feedback. Hereunder, is a photo of myself presenting some of the related work in PbD, threat analysis, and threat modeling.
Explaining the related research work before positioning my contribution.
Overall, I can say that there were some fantastic keynotes and excellent presentations from diverse Phd students. Especially, I liked the keynote “Privacy as Innovation opportunity” by Marc van Lieshout from Radboud University. In particular, I enjoyed his mentioning of Alan Westin’s privacy dimensions: reserve, intimacy, anonymity, and solitude; and how these are to different extents being hampered by privacy-evasive technologies, affecting the physical, individual, collective, and virtual dimensions of human beings. At the same time, I like his take on the increasing market of privacy, in particular with privacy service features such as activity monitoring, assessment manager, data mapping, etc.
My advice, if you are a doctoral student or interested in learning information privacy from a computer science or informatics standpoint, then I highly recommend you to attend the IFIP school at some point. Typically, there are ECTS credits for this course, (possibly 1.5 HP – 3 HP) if you attend and/or present your paper. In the meantime, check out my presentation (redacted version). The full version will be uploaded after the paper gets published.